Alleged breach of Orange exemplifies the economics cybercrime
The ransomware group Babuk claims to have breached the French telecommunication company Orange, and its Romanian subsidiary, resulting in the theft of 4.5 TB of data. According to Cybernews, Babuk threatens to publish 1 TB of the allegedly stolen data unless Orange agrees to negotiate.
Orange Romania contests such reports, saying the data was stolen from the company in a similar ransomware attack by HellCat group in February 2025.
Uncertainty and conflicting claims are not unusual to the persistent threat landscape large organizations must navigate. Orange, with its multiple locations, thousands of employees, and a publicly disclosed breach data, presents a relatively broad attack surface. But it’s important to note that ransomware operators are fundamentally opportunistic. They seek financial gain and will exploit any available vulnerability, regardless of a target’s sector or size.
Background on Babuk
Babuk, the group reportedly behind the attack, has undergone several transformations since its original form in 2021. After the release of its source code on underground forums, various actors adapted it into their own ransomware-as-a-service (RaaS) programs, leading to the emergence of Babuk2. This new iteration has published information on more than 45 victims in March 2025 alone, frequently targeting organizations that had previously suffered breaches. It has also been observed publishing data from previous breaches by other RaaS groups, as Orange Romania says in its case.
Motives
Cyberattacks on telecom companies inflict widespread damage. The breach of Orange by HellCat in February “impacted institutions, city halls, schools, hospitals, banks, insurers, transport and energy companies, as well as individuals,” according to Romania’s National Cybersecurity Directorate. However, these effects are likely collateral damage. Profit is the primary pursuit of most threat actors. This is probably just the side effect and is often not the main goal of the threat actors, who mostly operate in an opportunistic-financially motivated MO.
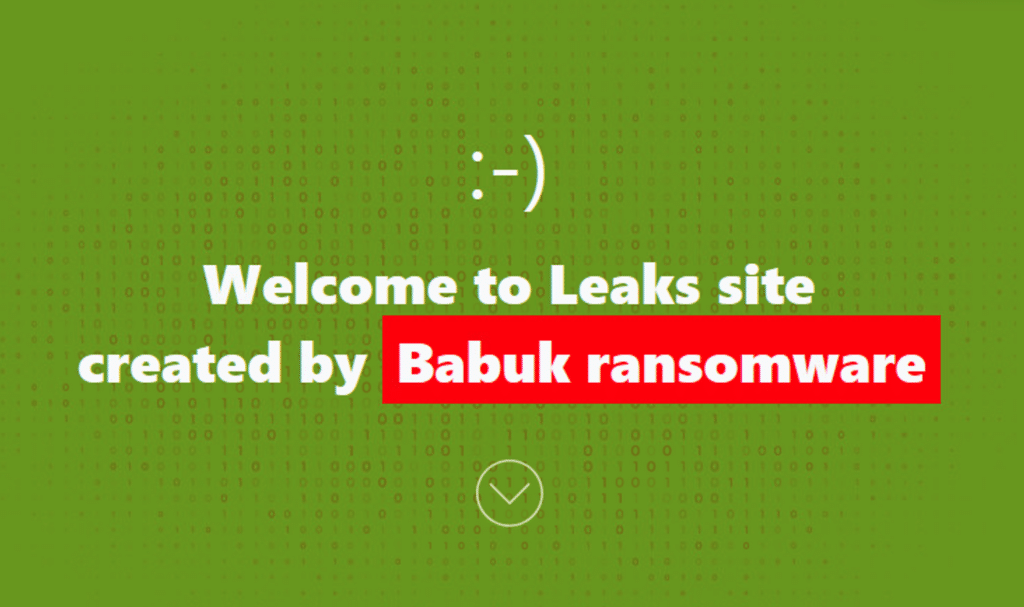
RaaS groups, while illegal and unethical, still adhere to a self-imposed standard of conduct, as can be gleaned from the Babuk leaksite ⬇️
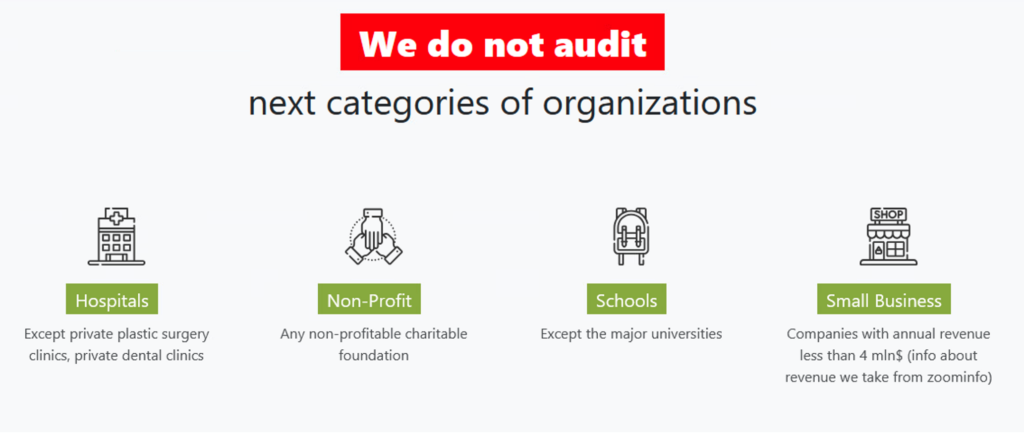
Audit is a euphemism for “hack.” These codes do not reflect goodwill. Rather, financially motivated threat actors have learned which targets tend to ratchet up the heat by law enforcement.
This pattern further suggests that Orange was hacked opportunistically—for money. Orange’s many locations and thousands of employees, along with coverage following its February breach, could lead threat actors to view the telecom as a legitimate, vulnerable target.
Even if Orange doesn’t pay the ransom, and company’s data is published, Babuk could leverage Orange’s name and news of the breach to burnish the Babuk brand in underground markets and recruit more affiliates to their program. The high-profile breach has already drawn significant attention in the media—and on the darknet.
Is Orange unique?
It is likely unfair to characterize Orange as inherently or uniquely vulnerable to cyberattacks, though the company has suffered multiple breaches. That stolen data was published in previous incidents could suggest Orange refused to pay those ransoms.
Other companies could opt to pay the ransom. Threat actors sometimes attempt to negotiate, using resources like ZoomInfo to adjust ransoms based on revenue, and even share the conclusions of their audit with the victim, allowing them to repair their security posture before gaps can be exploited by another threat actor.
Threat actors constantly adapt, evolve, and test their tools. So too must cybersecurity teams.
Recommended actions
To mitigate future threats, organizations must adopt a multilayered security approach. Implementing Endpoint Detection and Response (EDR/XDR), monitoring firewall logs, and deploying data loss prevention (DLP) solutions are crucial for early threat detection. Companies should also establish a Cyber Incident Response Team (CIRT), conduct regular risk assessments, and train employees on cybersecurity best practices.
It is not a question of if, but when an attack will occur, making proactive planning essential. A well-structured Incident Response Plan (IRP) and secure data backups can help organizations prepare for inevitable cyberattacks and reduce their operational impact. However, preparation alone is not enough. Effective Cyber Threat Intelligence (CTI) can help organizations anticipate threats, respond faster, and adapt smarter during an incident. Understanding who the adversary is, what their tactics are, and which emerging threats are relevant to a specific industry allows organizations to tailor defenses accordingly, proactively mitigating risks before they escalate into breaches.