Clear insight, stronger protection, faster action.
Extended Detection & Response (XDR)
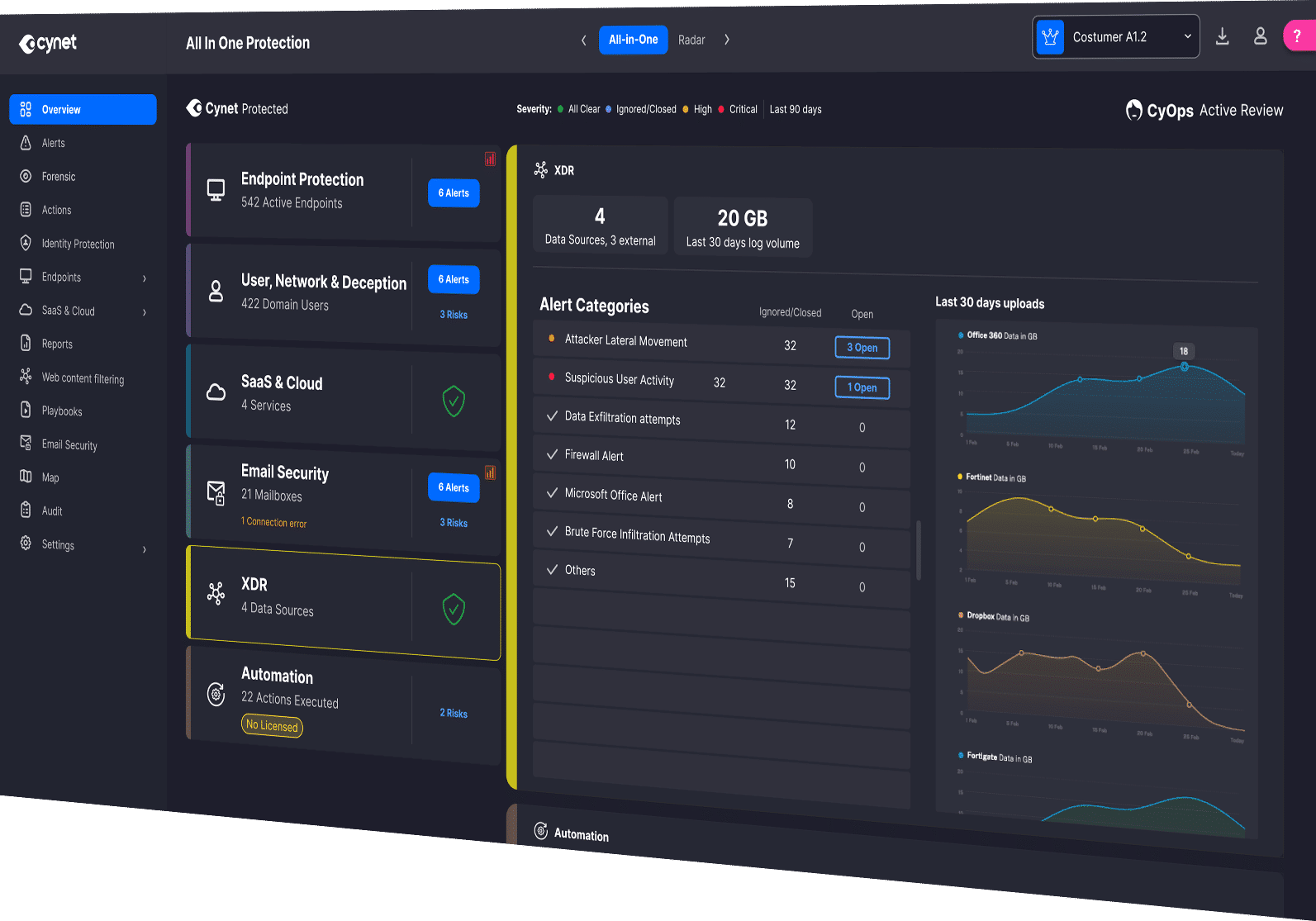
Cynet’s Extended Detection and Response (XDR) provides a unified platform that consolidates security data across all threat vectors.
By automating repetitive tasks, XDR reduces the number of management consoles, and provides a clearer, contextual view of threats across different layers of all environments.
Unify Your Defenses. Amplify Your Detection.
Cynet XDR eliminates blind spots by bringing together endpoint, identity, network, and cloud data into one automated platform.
Endpoints
Seamlessly integrate with endpoint devices to collect and analyze critical data such as process executions, file modifications, network connections, and system events in real-time.
Identity and Access Management (IAM) Systems
Monitor IAM systems, such as Active Directory, for suspicious user authentication events, group membership changes, and administrative actions.
Advanced Correlation
Employ sophisticated correlation techniques to analyze data from multiple sources, enabling the detection of complex attack patterns and potential threats that might otherwise go unnoticed.
Network Devices
Ingest data from network devices such as firewalls, routers, and switches, to enable comprehensive monitoring of network traffic, firewall logs, and intrusion detection prevention system (IDS/IPS) logs.
Real-Time Detection
Through continuous monitoring and real-time alerts, our platform enables organizations to detect security threats as they happen, minimizing the impact of cyber incidents on business operations.
Cloud Environments
Monitor user activities, file access events, and configuration changes within cloud environments.
Smarter Protection. Less Complexity.
Teams don’t have to juggle multiple tools or manage endless alerts. Cynet's unified, AI-powered platform combines XDR, 24x7 MDR, automated investigation and response, and identity protection to deliver enterprise-grade security that’s easy to deploy, manage, and scale.

